Clustering is a robust approach inside unsupervised machine studying that teams a given knowledge based mostly on their inherent similarities. Not like supervised studying strategies, equivalent to classification, which depend on pre-labeled knowledge to information the training course of, clustering operates on unlabeled knowledge. This implies there aren’t any predefined classes or labels and as a substitute, the algorithm discovers the underlying construction of the info with out prior data of what the grouping ought to appear to be.
The primary purpose of clustering is to arrange knowledge factors into clusters, the place knowledge factors inside the identical cluster have greater similarity to one another in comparison with these in numerous clusters. This distinction permits the clustering algorithm to type teams that replicate pure patterns within the knowledge. Primarily, clustering goals to maximise intra-cluster similarity whereas minimizing inter-cluster similarity. This method is especially helpful in use-cases the place you could discover hidden relationships or construction in knowledge, making it beneficial in areas equivalent to fraud detection and anomaly identification.
By making use of clustering, one can reveal patterns and insights that may not be apparent by different strategies, and its simplicity and suppleness makes it adaptable to all kinds of knowledge varieties and purposes.
A sensible utility of clustering is fraud detection in on-line techniques. Think about an instance the place a number of customers are making requests to an internet site, and every request contains particulars just like the IP tackle, time of the request, and transaction quantity.
Right here’s how clustering might help detect fraud:
- Think about that the majority customers are making requests from distinctive IP addresses, and their transaction patterns naturally differ.
- Nonetheless, if a number of requests come from the identical IP tackle and present comparable transaction patterns (equivalent to frequent, high-value transactions), it may point out {that a} fraudster is making a number of faux transactions from one supply.
By clustering all consumer requests based mostly on IP tackle and transaction conduct, we may detect suspicious clusters of requests that each one originate from a single IP. This could flag probably fraudulent exercise and assist in taking preventive measures.
An instance diagram that visually demonstrates the idea of clustering is proven within the determine beneath.
Think about you could have knowledge factors representing transaction requests, plotted on a graph the place:
- X-axis: Variety of requests from the identical IP tackle.
- Y-axis: Common transaction quantity.
On the left facet, now we have the uncooked knowledge. With out labels, we would already see some patterns forming. On the proper, after making use of clustering, the info factors are grouped into clusters, with every cluster representing a special consumer conduct.
To group knowledge successfully, we should outline a similarity measure, or metric, that quantifies how shut knowledge factors are to one another. This similarity could be measured in a number of methods, relying on the info’s construction and the insights we intention to find. There are two key approaches to measuring similarity — guide similarity measures and embedded similarity measures.
A guide similarity measure includes explicitly defining a mathematical formulation to match knowledge factors based mostly on their uncooked options. This technique is intuitive and we are able to use distance metrics like Euclidean distance, cosine similarity, or Jaccard similarity to guage how comparable two factors are. For example, in fraud detection, we may manually compute the Euclidean distance between transaction attributes (e.g transaction quantity, frequency of requests) to detect clusters of suspicious conduct. Though this method is comparatively simple to arrange, it requires cautious choice of the related options and should miss deeper patterns within the knowledge.
Alternatively, an embedded similarity measure leverages the ability of machine studying fashions to create discovered representations, or embeddings of the info. Embeddings are vectors that seize advanced relationships within the knowledge and could be generated from fashions like Word2Vec for textual content or neural networks for photos. As soon as these embeddings are computed, similarity could be measured utilizing conventional metrics like cosine similarity, however now the comparability happens in a reworked, lower-dimensional area that captures extra significant data. Embedded similarity is especially helpful for advanced knowledge, equivalent to consumer conduct on web sites or textual content knowledge in pure language processing. For instance, in a film or advertisements suggestion system, consumer actions could be embedded into vectors, and similarities on this embedding area can be utilized to advocate content material to comparable customers.
Whereas guide similarity measures present transparency and higher management on characteristic choice and setup, embedded similarity measures give the power to seize deeper and extra summary relationships within the knowledge. The selection between the 2 is dependent upon the complexity of the info and the precise targets of the clustering process. You probably have well-understood, structured knowledge, a guide measure could also be enough. But when your knowledge is wealthy and multi-dimensional, equivalent to in textual content or picture evaluation, an embedding-based method might give extra significant clusters. Understanding these trade-offs is essential to choosing the proper method to your clustering process.
In instances like fraud detection, the place the info is commonly wealthy and based mostly on conduct of consumer exercise, an embedding-based method is usually more practical for capturing nuanced patterns that would sign dangerous exercise.
Coordinated fraudulent assault behaviors usually exhibit particular patterns or traits. For example, fraudulent exercise might originate from a set of comparable IP addresses or depend on constant, repeated ways. Detecting these patterns is essential for sustaining the integrity of a system, and clustering is an efficient approach for grouping entities based mostly on shared traits. This helps the identification of potential threats by analyzing the collective conduct inside clusters.
Nonetheless, clustering alone will not be sufficient to precisely detect fraud, as it might probably additionally group benign actions alongside dangerous ones. For instance, in a social media atmosphere, customers posting innocent messages like “How are you at present?” is likely to be grouped with these engaged in phishing assaults. Therefore, extra standards is important to separate dangerous conduct from benign actions.
To handle this, we introduce the Behavioral Evaluation and Cluster Classification System (BACCS) as a framework designed to detect and handle abusive behaviors. BACCS works by producing and classifying clusters of entities, equivalent to particular person accounts, organizational profiles, and transactional nodes, and could be utilized throughout a variety of sectors together with social media, banking, and e-commerce. Importantly, BACCS focuses on classifying behaviors somewhat than content material, making it extra appropriate for figuring out advanced fraudulent actions.
The system evaluates clusters by analyzing the mixture properties of the entities inside them. These properties are usually boolean (true/false), and the system assesses the proportion of entities exhibiting a particular attribute to find out the general nature of the cluster. For instance, a excessive share of newly created accounts inside a cluster may point out fraudulent exercise. Primarily based on predefined insurance policies, BACCS identifies combos of property ratios that recommend abusive conduct and determines the suitable actions to mitigate the risk.
The BACCS framework affords a number of benefits:
- It permits the grouping of entities based mostly on behavioral similarities, enabling the detection of coordinated assaults.
- It permits for the classification of clusters by defining related properties of the cluster members and making use of customized insurance policies to establish potential abuse.
- It helps computerized actions towards clusters flagged as dangerous, making certain system integrity and enhancing safety towards malicious actions.
This versatile and adaptive method permits BACCS to constantly evolve, making certain that it stays efficient in addressing new and rising types of coordinated assaults throughout totally different platforms and industries.
Let’s perceive extra with the assistance of an analogy: Let’s say you could have a wagon filled with apples that you simply wish to promote. All apples are put into baggage earlier than being loaded onto the wagon by a number of employees. A few of these employees don’t such as you, and attempt to fill their baggage with bitter apples to mess with you. That you must establish any bag that may include bitter apples. To establish a bitter apple you could examine whether it is delicate, the one drawback is that some apples are naturally softer than others. You resolve the issue of those malicious employees by opening every bag and selecting out 5 apples, and also you examine if they’re delicate or not. If virtually all of the apples are delicate it’s seemingly that the bag comprises bitter apples, and you place it to the facet for additional inspection afterward. When you’ve recognized all of the potential baggage with a suspicious quantity of softness you pour out their contents and pick the wholesome apples that are arduous and throw away all of the delicate ones. You’ve now minimized the chance of your prospects taking a chunk of a bitter apple.
BACCS operates in an analogous method; as a substitute of apples, you could have entities (e.g., consumer accounts). As an alternative of dangerous employees, you could have malicious customers, and as a substitute of the bag of apples, you could have entities grouped by frequent traits (e.g., comparable account creation occasions). BACCS samples every group of entities and checks for indicators of malicious conduct (e.g., a excessive price of coverage violations). If a bunch reveals a excessive prevalence of those indicators, it’s flagged for additional investigation.
Similar to checking the supplies within the classroom, BACCS makes use of predefined alerts (additionally known as properties) to evaluate the standard of entities inside a cluster. If a cluster is discovered to be problematic, additional actions could be taken to isolate or take away the malicious entities. This technique is versatile and might adapt to new kinds of malicious conduct by adjusting the factors for flagging clusters or by creating new kinds of clusters based mostly on rising patterns of abuse.
This analogy illustrates how BACCS helps preserve the integrity of the atmosphere by proactively figuring out and mitigating potential points, making certain a safer and extra dependable area for all respectable customers.
The system affords quite a few benefits:
- Higher Precision: By clustering entities, BACCS offers robust proof of coordination, enabling the creation of insurance policies that will be too imprecise if utilized to particular person entities in isolation.
- Explainability: Not like some machine studying methods, the classifications made by BACCS are clear and comprehensible. It’s simple to hint and perceive how a specific choice was made.
- Fast Response Time: Since BACCS operates on a rule-based system somewhat than counting on machine studying, there is no such thing as a want for intensive mannequin coaching. This leads to sooner response occasions, which is vital for speedy problem decision.
BACCS is likely to be the proper resolution to your wants in the event you:
- Give attention to classifying conduct somewhat than content material: Whereas many clusters in BACCS could also be fashioned round content material (e.g., photos, e mail content material, consumer telephone numbers), the system itself doesn’t classify content material straight.
- Deal with points with a comparatively excessive frequancy of occurance: BACCS employs a statistical method that’s only when the clusters include a major proportion of abusive entities. It will not be as efficient for dangerous occasions that sparsely happen however is extra suited to extremely prevalent issues equivalent to spam.
- Cope with coordinated or comparable conduct: The clustering sign primarily signifies coordinated or comparable conduct, making BACCS notably helpful for addressing most of these points.
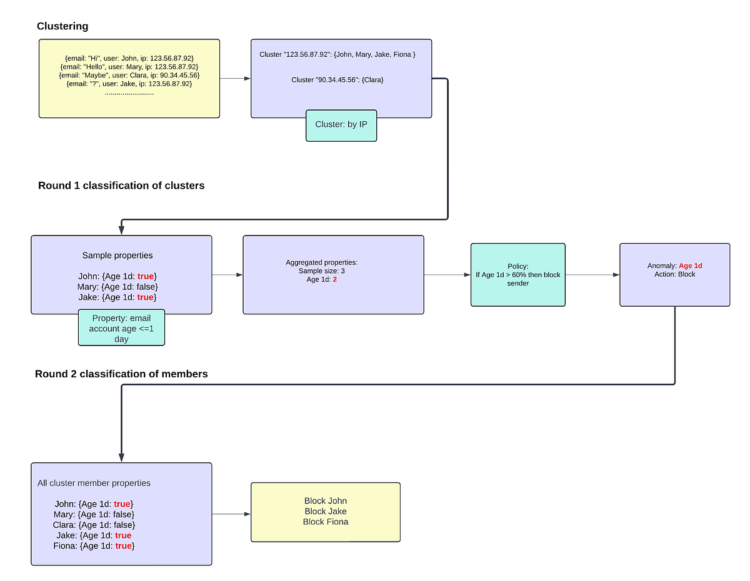
Right here’s how one can incorporate BACCS framework in an actual manufacturing system:
- When entities have interaction in actions on a platform, you construct an remark layer to seize this exercise and convert it into occasions. These occasions can then be monitored by a system designed for cluster evaluation and actioning.
- Primarily based on these occasions, the system must group entities into clusters utilizing varied attributes — for instance, all customers posting from the identical IP tackle are grouped into one cluster. These clusters ought to then be forwarded for additional classification.
- Throughout the classification course of, the system must compute a set of specialised boolean alerts for a pattern of the cluster members. An instance of such a sign could possibly be whether or not the account age is lower than a day. The system then aggregates these sign counts for the cluster, equivalent to figuring out that, in a pattern of 100 customers, 80 have an account age of lower than in the future.
- These aggregated sign counts needs to be evaluated towards insurance policies that decide whether or not a cluster seems to be anomalous and what actions needs to be taken whether it is. For example, a coverage may state that if greater than 60% of the members in an IP cluster have an account age of lower than a day, these members ought to bear additional verification.
- If a coverage identifies a cluster as anomalous, the system ought to establish all members of the cluster exhibiting the alerts that triggered the coverage (e.g., all members with an account age of lower than in the future).
- The system ought to then direct all such customers to the suitable motion framework, implementing the motion specified by the coverage (e.g., additional verification or blocking their account).
Sometimes, your complete course of from exercise of an entity to the applying of an motion is accomplished inside a number of minutes. It’s additionally essential to acknowledge that whereas this technique offers a framework and infrastructure for cluster classification, purchasers/organizations want to produce their very own cluster definitions, properties, and insurance policies tailor-made to their particular area.
Let’s take a look at the instance the place we attempt to mitigate spam by way of clustering customers by ip once they ship an e mail, and blocking them if >60% of the cluster members have account age lower than a day.
Members can already be current within the clusters. A re-classification of a cluster could be triggered when it reaches a sure dimension or has sufficient modifications because the earlier classification.
When choosing clustering standards and defining properties for customers, the purpose is to establish patterns or behaviors that align with the precise dangers or actions you’re attempting to detect. For example, in the event you’re engaged on detecting fraudulent conduct or coordinated assaults, the factors ought to seize traits which might be usually shared by malicious actors. Listed below are some elements to think about when selecting clustering standards and defining consumer properties:
The clustering standards you select ought to revolve round traits that characterize conduct prone to sign threat. These traits may embrace:
- Time-Primarily based Patterns: For instance, grouping customers by account creation occasions or the frequency of actions in a given time interval might help detect spikes in exercise which may be indicative of coordinated conduct.
- Geolocation or IP Addresses: Clustering customers by their IP tackle or geographical location could be particularly efficient in detecting coordinated actions, equivalent to a number of fraudulent logins or content material submissions originating from the identical area.
- Content material Similarity: In instances like misinformation or spam detection, clustering by the similarity of content material (e.g., comparable textual content in posts/emails) can establish suspiciously coordinated efforts.
- Behavioral Metrics: Traits just like the variety of transactions made, common session time, or the kinds of interactions with the platform (e.g., likes, feedback, or clicks) can point out uncommon patterns when grouped collectively.
The secret’s to decide on standards that aren’t simply correlated with benign consumer conduct but additionally distinct sufficient to isolate dangerous patterns, which is able to result in more practical clustering.
Defining Consumer Properties
When you’ve chosen the factors for clustering, defining significant properties for the customers inside every cluster is crucial. These properties needs to be measurable alerts that may aid you assess the probability of dangerous conduct. Frequent properties embrace:
- Account Age: Newly created accounts are inclined to have a better threat of being concerned in malicious actions, so a property like “Account Age < 1 Day” can flag suspicious conduct.
- Connection Density: For social media platforms, properties just like the variety of connections or interactions between accounts inside a cluster can sign irregular conduct.
- Transaction Quantities: In instances of monetary fraud, the common transaction dimension or the frequency of high-value transactions could be key properties to flag dangerous clusters.
Every property needs to be clearly linked to a conduct that would point out both respectable use or potential abuse. Importantly, properties needs to be boolean or numerical values that enable for simple aggregation and comparability throughout the cluster.
One other superior technique is utilizing a machine studying classifier’s output as a property, however with an adjusted threshold. Usually, you’d set a excessive threshold for classifying dangerous conduct to keep away from false positives. Nonetheless, when mixed with clustering, you may afford to decrease this threshold as a result of the clustering itself acts as a further sign to bolster the property.
Let’s take into account that there’s a mannequin X, that catches rip-off and disables e mail accounts which have mannequin X rating > 0.95. Assume this mannequin is already stay in manufacturing and is disabling dangerous e mail accounts at threshold 0.95 with 100% precision. We’ve got to extend the recall of this mannequin, with out impacting the precision.
- First, we have to outline clusters that may group coordinated exercise collectively. Let’s say we all know that there’s a coordinated exercise occurring, the place dangerous actors are utilizing the identical topic line however totally different e mail ids to ship scammy emails. So utilizing BACCS, we are going to type clusters of e mail accounts that each one have the identical topic identify of their despatched emails.
- Subsequent, we have to decrease the uncooked mannequin threshold and outline a BACCS property. We are going to now combine mannequin X into our manufacturing detection infra and create property utilizing lowered mannequin threshold, say 0.75. This property can have a price of “True” for an e mail account that has mannequin X rating >= 0.75.
- Then we’ll outline the anomaly threshold and say, if 50% of entities within the marketing campaign identify clusters have this property, then classify the clusters as dangerous and take down advert accounts which have this property as True.
So we primarily lowered the mannequin’s threshold and began disabling entities particularly clusters at considerably decrease threshold than what the mannequin is presently implementing at, and but could be certain the precision of enforcement doesn’t drop and we get a rise in recall. Let’s perceive how –
Supposed now we have 6 entities which have the identical topic line, which have mannequin X rating as follows:
If we use the uncooked mannequin rating (0.95) we’d have disabled 2/6 e mail accounts solely.
If we cluster entities on topic line textual content, and outline a coverage to search out dangerous clusters having higher than 50% entities with mannequin X rating >= 0.75, we’d have taken down all these accounts:
So we elevated the recall of enforcement from 33% to 83%. Primarily, even when particular person behaviors appear much less dangerous, the truth that they’re a part of a suspicious cluster elevates their significance. This mixture offers a robust sign for detecting dangerous exercise whereas minimizing the probabilities of false positives.
By decreasing the edge, you enable the clustering course of to floor patterns that may in any other case be missed in the event you relied on classification alone. This method takes benefit of each the granular insights from machine studying fashions and the broader behavioral patterns that clustering can establish. Collectively, they create a extra sturdy system for detecting and mitigating dangers and catching many extra entities whereas nonetheless protecting a decrease false constructive price.
Clustering methods stay an vital technique for detecting coordinated assaults and making certain system security, notably on platforms extra liable to fraud, abuse or different malicious actions. By grouping comparable behaviors into clusters and making use of insurance policies to take down dangerous entities from such clusters, we are able to detect and mitigate dangerous exercise and guarantee a safer digital ecosystem for all customers. Selecting extra superior embedding-based approaches helps characterize advanced consumer behavioral patterns higher than guide strategies of similarity detection measures.
As we proceed advancing our safety protocols, frameworks like BACCS play a vital function in taking down giant coordinated assaults. The mixing of clustering with behavior-based insurance policies permits for dynamic adaptation, enabling us to reply swiftly to new types of abuse whereas reinforcing belief and security throughout platforms.
Sooner or later, there’s a large alternative for additional analysis and exploration into complementary methods that would improve clustering’s effectiveness. Strategies equivalent to graph-based evaluation for mapping advanced relationships between entities could possibly be built-in with clustering to supply even greater precision in risk detection. Furthermore, hybrid approaches that mix clustering with machine studying classification is usually a very efficient method for detecting malicious actions at greater recall and decrease false constructive price. Exploring these strategies, together with steady refinement of present strategies, will be sure that we stay resilient towards the evolving panorama of digital threats.